What is Congestion Control? Describe the Congestion Control Algorithm commonly used - Computer Notes

Congestion Control in Computer Network -Leaky Bucket Algorithm/Safad Ismail,Asst.Professor,CASM,IHRD - YouTube
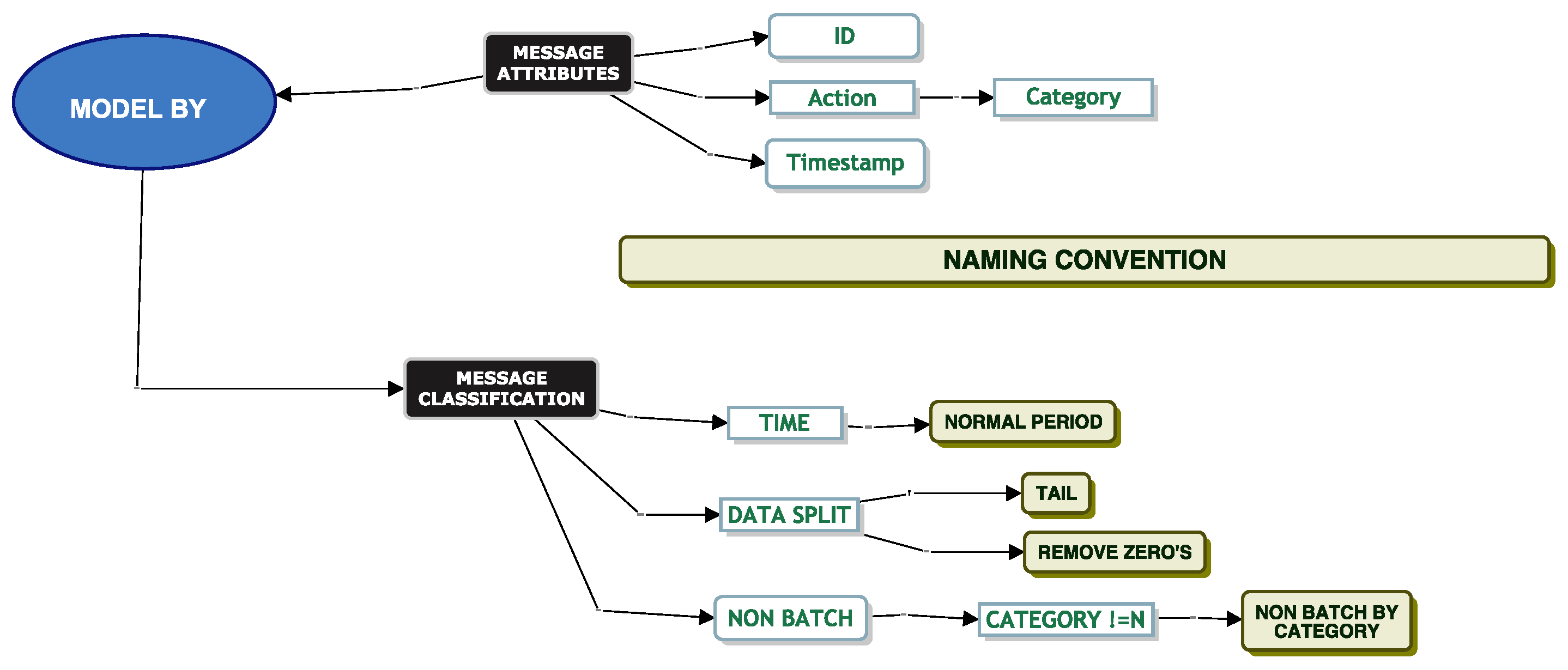
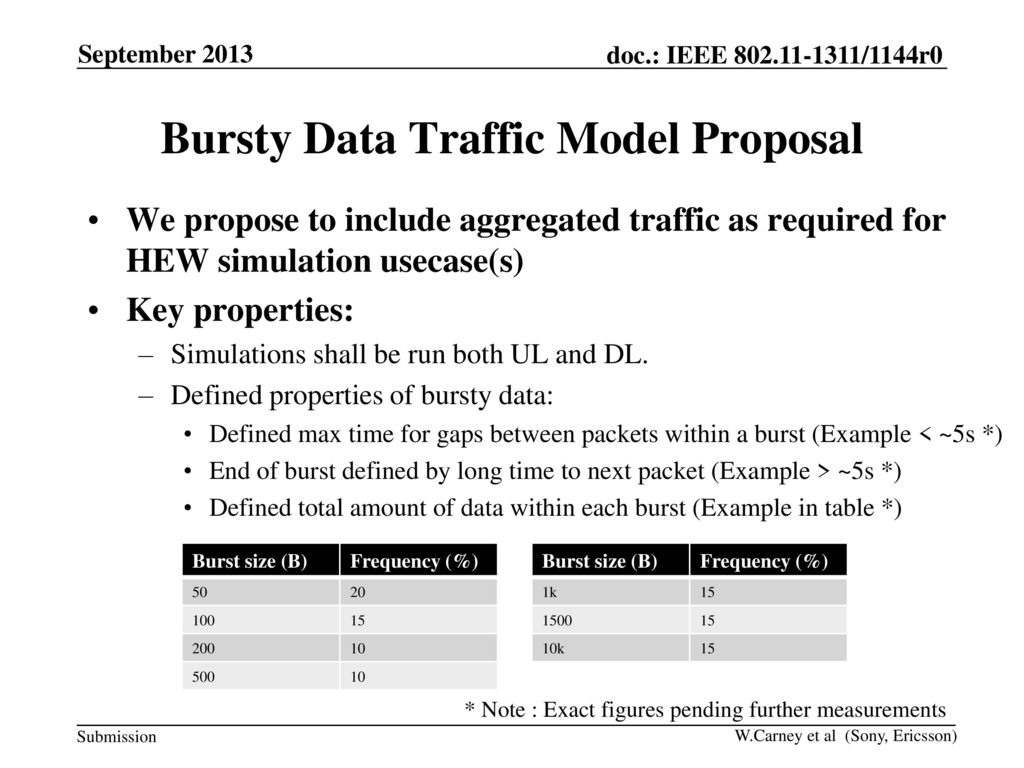
Future Internet | Free Full-Text | A Framework to Model Bursty Electronic Data Interchange Messages for Queueing Systems
AWS re:Invent 2018: Build High-Throughput, Bursty Data Apps with Amazon SQS, SNS, & Lambda (API306) - YouTube
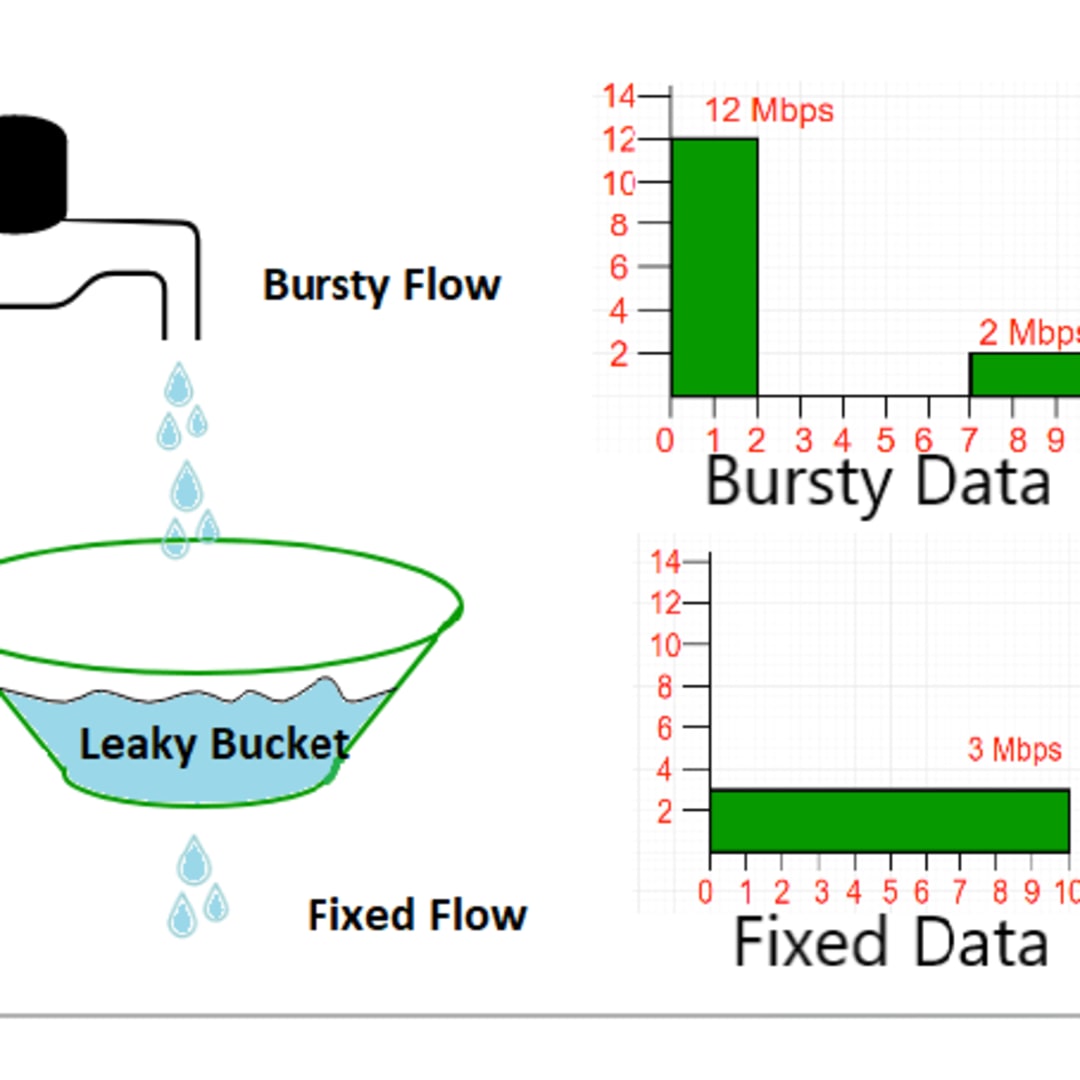
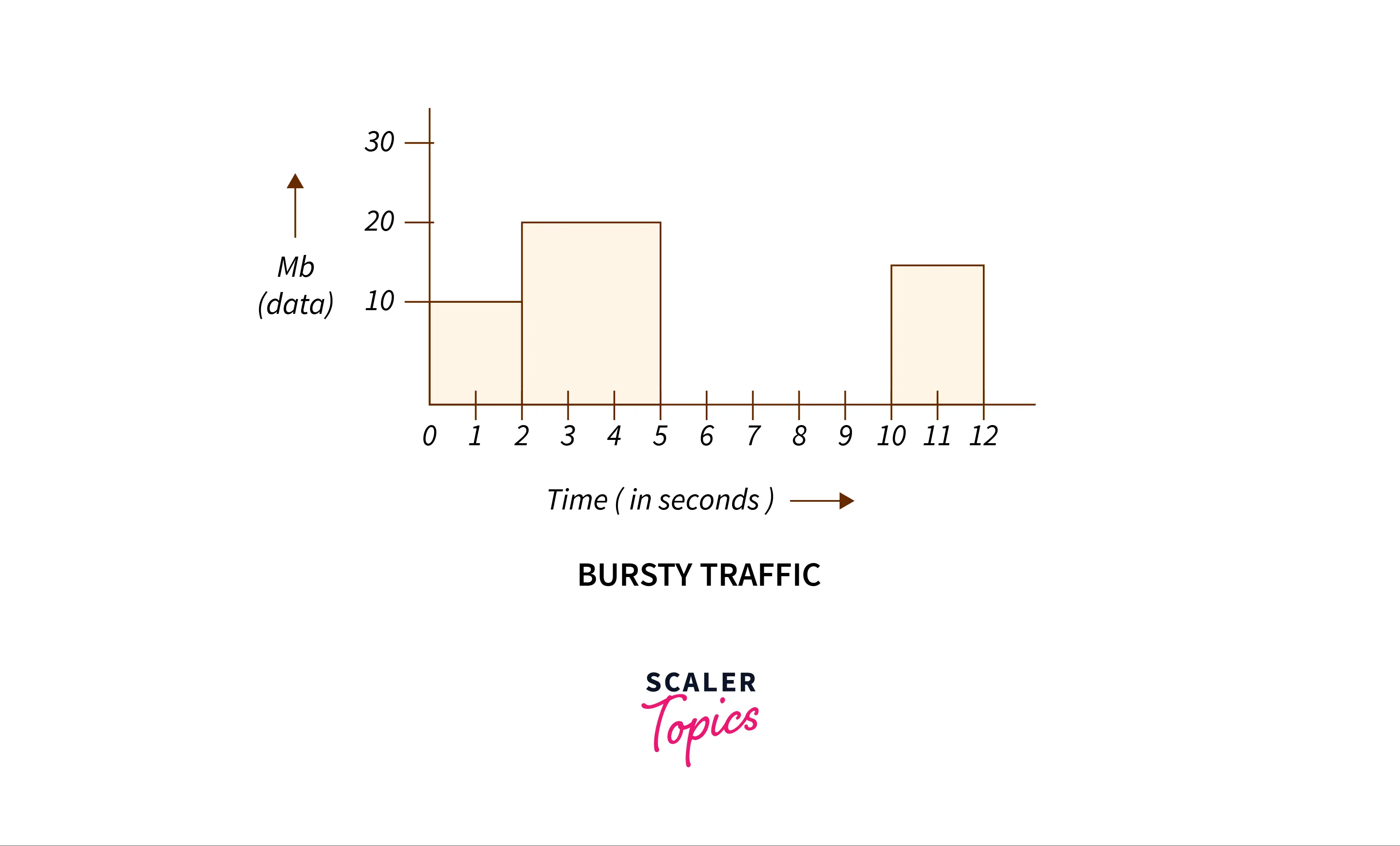
NETWORK LAYER. CONGESTION CONTROL In congestion control we try to avoid traffic congestion. Traffic Descriptor Traffic descriptors are qualitative values. - ppt download

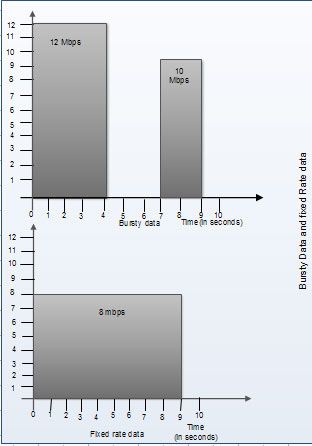
Bursty nature of streaming traffic In UTRAN there are basically two... | Download Scientific Diagram

Adaptive Frequency Counting over Bursty Data Streams Bill Lin, Wai-Shing Ho, Ben Kao and Chun-Kit Chui Form CIDM ppt download







![1. A typical Bursty internet traffic network system [9] | Download Scientific Diagram 1. A typical Bursty internet traffic network system [9] | Download Scientific Diagram](https://www.researchgate.net/profile/Oyebayo-Olaniran/publication/318727778/figure/fig1/AS:631652921405465@1527609200355/A-typical-Bursty-internet-traffic-network-system-9.png)